Whether a private home network or company infrastructure - without subnetting, the Internet would literally collapse. The division of IP address spaces into logical subnets is the basis for efficient, secure and scalable networks. But how exactly does subnetting work and why is it so important?
This article is an updated version.
Definition subnetting
With subnetting, subnets are formed within a contiguous address space of IP addresses.
A subnet is a physical or logical segment of a network in which IP addresses with the same network address are used. These subnets can be connected to each other via routers and then form a large, coherent network.
Reasons for subnetting
Why is subnetting important?
- Subnetting can be used to separate networks from each other and it is possible to assign private IP addresses twice.
- Network Relief: The larger a network is, the more devices want to send their data packets at the same time. This increases the network load. Without subnetting, the internet would collapse within seconds due to Hello packets. Conversely, this means that with more subnets, there is less traffic within the networks or between hosts that have nothing to do with each other.
- Improved network performance: If the sender and receiver of the data packets are in the same network, the data packets do not have to pass through different networks and routers. This also increases network performance.
- Structured address assignment: System administrators can create a logical structure for the allocation of IP addresses. This improves clarity and makes their work much easier.
- More security: Subnetting increases security because individual networks are separated from each other. Attacks must first reach other network sections to spread further. (Firewalls in the connecting network routers).
These advantages are based on the fundamental concept of IP addressing. To understand how subnetting works, we must first look at the structure of IP addresses.
Structure of an IP address: Network ID and host ID
An IP address is a unique sequence of numbers that is assigned to each device in a TCP/IP network and there are currently two commonly used variants of IP addresses: IPv4 and IPv6. IPv4 is still most commonly used for private networks and is easier to understand than IPv6. For this article we will therefore limit ourselves here to IPv4. You can find more knowledge about advantages of IPv6 in our "IPv6: Explanation, Advantages, Outlook" article.
An IP address essentially consists of two elements:
- the network address
- and the host address
Information about the network address is important for the delivery of data packets. The network address or Net-IP roughly comparable to a postal code. It determines a subnet in whose area the host address falls. The host address (Host ID) in turn is comparable to a street/house number of a destination address. It is assigned to a special host within the subnet.
All computers in a local network, for example in the office network, where the network share is the same, are in the same subnet and can communicate with each other. In this case, the network address is identical for the source and destination addresses and the data packet can be delivered within the subnet without further routing. If the network addresses are different, the data packet must be routed via the standard gateway (default gateway) to a different subnet. Requests and data packets are therefore first sent to the Net-IP of a specific router, as in a letter sorting system, which then distributes them to the respective host.
IPv4
An IPv4 address consists of 4 bytes (32 bits), which are represented by 4 octets. Each 8 bits are separated by a dot using a 3-digit numerical sequence (e.g. 192.168.12.0).
In order to understand how subnetting works, it is important to know both forms of representation of an IP address - the decimal notation readable by humans and the binary notation relevant for computers.
Decimal vs. bit notation
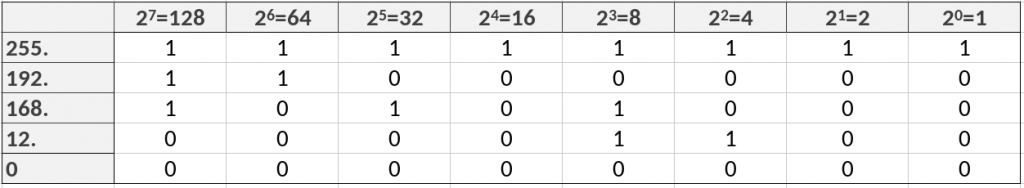
We stay with the example IP address: 192.168.12.0 Each octet consists of 8 bits each. In the binary system, each individual bit stands for a number that results from the power (0-7) of 2. Because for each bit position the computer can receive two possible signals: Current on (1) or Current off (0). This results in 2(to the power of)8=256 variants. Each octet can thus take the minimum value 0 and the maximum numerical value of 255.
The decimal value of the octet results from the sum of the activated bits. At the maximum value 255 all bit positions have the value 1. For the first octet in our example with the value 192 the first two bits are set to 1 and the rest to zero. The value 168 (2nd octet) results from the sum of the bit values 128, 32 and 8. and so on.
With this understanding of the IP address structure, we can now turn our attention to the subnet mask - the crucial element that determines how an IP address is divided up.
What is the subnet mask?
The subnet mask determines the network portion (subnet) and the remaining host portion of an IP address. The subnet mask thus indicates where this separation of network address and host address should take place and how many bits remain for the host part. There are two common notations for the subnet mask, one with octets and one as a suffix notation:
Example: 192.168.12.15 / 255.255.255.0 OR
192.168.12.15 / 24 (Suffix notation determines net prefix)
The subnet mask is always separated by a "/" after the IP address. The "255" values in the longer form indicate that all bit values here are assigned 1 for the network portion. They are not available for the host assignment. The "zero" range in the rear octets thus determines the remaining host portion for the IP assignment.
In suffix notation, the suffix (the number after the "/") determines the network prefix, i.e. the number of bits intended for the network address. With a suffix of 24, 8 bits (1 octet) remain for the host part. The first 24 places are occupied by 1 for the network. However, the subnet mask is readable for machines in binary notation. Here, the subnet mask also consists of a contiguous sequence of 1 and 0.
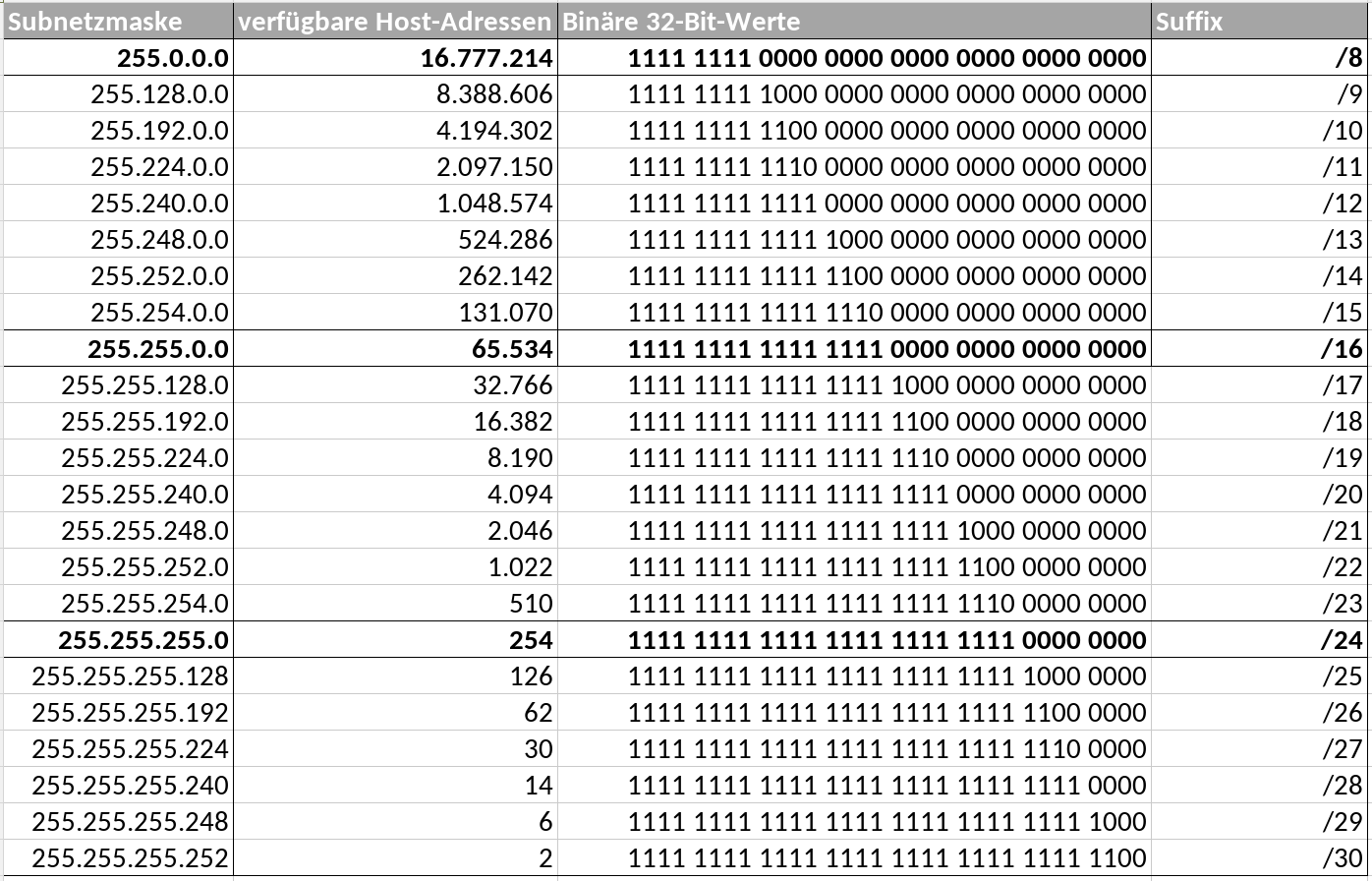
The subnet mask therefore determines how many IP addresses are available for hosts in a subnet. The following table shows the most common subnet masks and the respective number of usable IP addresses. At 32 bits, the subnet mask is just as long as any IP address. The suffix after the IP address mentioned above indicates how many 1s follow one after the other within the subnet mask in bit notation. 24 therefore means 255.255.255.0 for the network ID.
A closer look reveals this: The number of available host addresses is always two less than mathematically possible. There is an important reason for this - let's take a look at a concrete example:
Example: Network address & broadcast address
Let's take the /30 subnet as an example - it has the smallest possible usable network share, which can only include two host IPs. Why are there only 2 IP host addresses for /30 and not 4 (22=4)? This is because the first and last IP addresses are required to define the address range. The smallest host IP, here".252" stands for the designation of the Network address and ".255" for the Broadcast address (BC address). These addresses are therefore occupied and cannot be assigned to any host. For this reason, the number of available IP addresses within a subnet is reduced by two IPs each for the network and broadcast IP address.
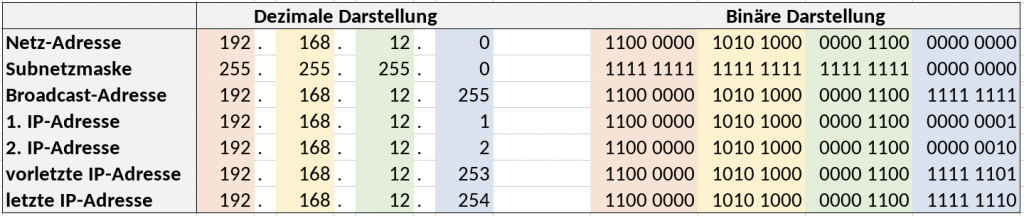
In the example above, the network address or network address would be 192.168.12.0 and the broadcast address 192.168.12.255. Data packets are sent to all active hosts simultaneously via the broadcast address, e.g. so-called "Hello packets", which a host sends when it is activated. Every client in the network (every end device, every router and every switch) receives the request or must provide a response. The first free host address in the example would therefore be 192.168.12.1 and the last possible host address would be 192.168.12.254.
However, there are also exceptions: If broadcasts can be dispensed with in communication between subnets, this is possible in so-called transfer networks between routers, for example. Here, the allocation of /31 subnets would be possible in order to save on IPv4 addresses in particular.
Conclusion
Subnetting is a fundamental concept of modern network technology. It improves network performance, increases security through segmentation and enables structured address allocation. Without subnetting, today's Internet would be unthinkable in its current form, as the network load would lead to a collapse within seconds.
With the basic knowledge of IP addresses, subnet masks and bit notation provided here, system administrators can set up efficient and secure network structures. We hope that this article will also help IT beginners to better understand how the internet and hosting processes work.
ScaleUp is a business hosting company with over 27 years of hosting experience. We operate state-of-the-art colocation and server housing spaces as well as cloud infrastructures certified according to the IaaS-SCS standard based on open source technologies (OpenStack, Kubernetes) at several data center locations in Hamburg, Berlin, Nuremberg and Düsseldorf. We are happy to assist you available for queries.

